Share
IT SPARC Cast
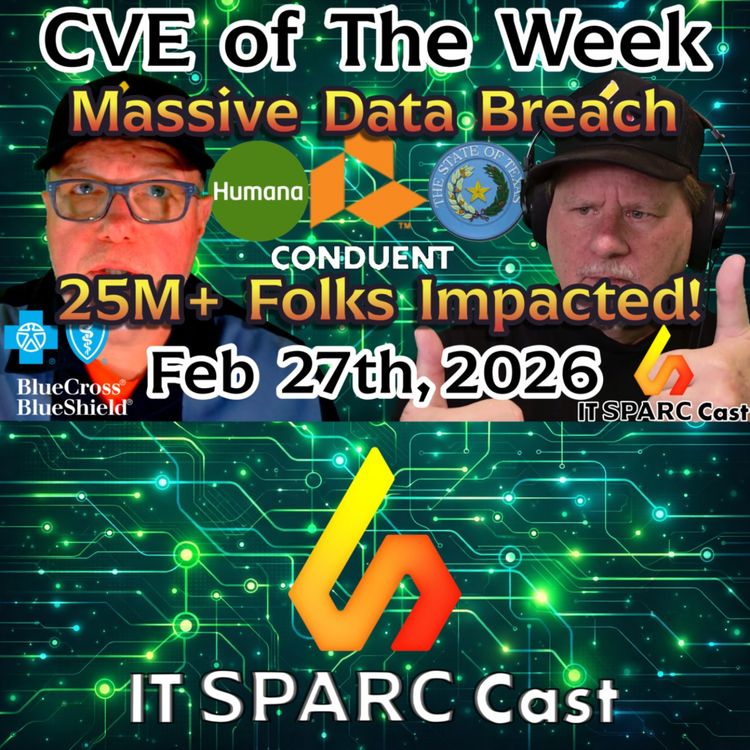
Conduent Ransomware Breach Hits 25 Million – HR & Benefits Data Exposed
In this episode of IT SPARC Cast – CVE of the Week, John Barger and Lou Schmidt break down a massive ransomware-driven data breach impacting Conduent, a major business process services provider that handles public sector programs, healthcare benefits processing, and corporate HR services.
What began as reports of a 10.5 million record breach has now escalated to an estimated 25 million impacted individuals, with the ransomware group SafePay claiming responsibility and alleging over 8 terabytes of data exfiltrated.
⸻
🔎 What Happened?
Conduent, which provides backend processing for government assistance programs and health benefits, confirmed that sensitive personal and corporate information may have been exposed.
Reported exposed data includes:
• Names
• Dates of birth
• Addresses
• Social Security numbers
• Employment records
• Financial information
• Medical and health insurance details
• Internal business documents
SafePay ransomware actors reportedly gained access through compromised credentials and then moved laterally through Conduent’s systems.
This is a textbook example of a chained cyberattack, where one small compromise enables full-scale enterprise exposure.
⸻
🌎 Scope of the Impact
The breach affects multiple U.S. states and programs, including:
• Texas (~15.4 million impacted)
• Oregon (~10.5 million impacted)
• Delaware
• Massachusetts
• New Hampshire
• Georgia
• South Carolina
• New Jersey
• Maine
• New Mexico
Programs potentially affected:
• Medicaid
• SNAP / EBT food assistance
• Unemployment benefits
• Health insurance processing (including Blue Cross Blue Shield and Humana)
• Corporate employee benefit programs
Additionally, approximately 17,000 Volvo Group North America employees may have been impacted.
⸻
⚠ Why This Matters for Enterprise IT
This is not “just” a public-sector breach.
Many private companies rely on Conduent for backend benefits processing. If your organization uses:
• Blue Cross Blue Shield
• Humana
• Third-party HR / benefits processors
You must immediately:
• Contact your HR and benefits teams
• Request incident briefings from vendors
• Determine if employee data was exposed
• Prepare remediation and communication plans
⸻
🔐 Security Lessons
• Credential compromise remains a primary entry point
• Lateral movement amplifies initial footholds
• Ransomware groups continue combining encryption with large-scale data exfiltration
• Transparency and timely disclosure are critical
Conduent acknowledged the breach, engaged forensic investigators, and notified impacted parties — a necessary and responsible response.
⸻
💬 Listener Feedback
The episode also includes feedback from Kevin regarding last week’s Apple iOS 26 patch discussion. While some users hesitate to upgrade due to UI and stability concerns, security patches addressing critical vulnerabilities must take priority.
⸻
🔗 Connect With Us
IT SPARC Cast
@ITSPARCCast on X
https://www.linkedin.com/company/sparc-sales/ on LinkedIn
John Barger
@john_Video on X
https://www.linkedin.com/in/johnbarger/ on LinkedIn
Lou Schmidt
@loudoggeek on X
https://www.linkedin.com/in/louis-schmidt-b102446/ on LinkedIn
More episodes
View all episodes

29. North Korea’s Fake IT Workers: The Insider Threat Hiding in Plain Sight
14:42||Season 2, Ep. 29In this episode of IT SPARC Cast – CVE of the Week, John Barger and Lou Schmidt break down a rapidly growing cybersecurity threat: North Korean operatives posing as remote IT workers inside enterprise environments.These actors are not just external attackers — they are getting hired, accessing corporate systems, and creating persistent insider threats that are extremely difficult to detect.The episode explores how the scheme works, why traditional security controls fail, and what enterprise IT teams must do to defend against this evolving attack vector.⸻📝 Show NotesA new cybersecurity threat is emerging that flips the traditional attack model on its head.Instead of breaking into your network, attackers are getting hired into your company.In this episode of IT SPARC Cast – CVE of the Week, John Barger and Lou Schmidt analyze the growing threat of North Korean IT worker schemes, where operatives pose as legitimate remote employees to gain direct access to enterprise systems.⸻🔎 How the Scheme WorksThreat actors: • Apply for remote IT jobs using stolen or synthetic identities • Pass interviews and onboarding processes • Gain legitimate access to corporate systems • Use that access to exfiltrate data, generate revenue, or stage future attacksThese individuals often work through: • VPN masking • Proxy networks • Identity laundering through third partiesOnce inside, they operate as trusted insiders, making detection significantly more difficult than traditional external threats.⸻⚠ Why This Is So DangerousThis is not a vulnerability in software — it’s a failure in process, identity, and trust models.Key risks include: • Direct access to internal systems and data • Ability to bypass perimeter security controls • Long-term persistence without detection • Potential for data exfiltration, espionage, or ransomware stagingUnlike typical breaches, these actors are: • Authenticated • Approved • Operating under legitimate credentials⸻🏢 Enterprise IT ImpactThis threat directly impacts: • Remote-first organizations • Companies hiring globally • Teams using contractors or third-party staffing firms • Organizations without strict identity verification processesIf your company hires remote developers, engineers, or IT staff — this is your problem.⸻🔐 Key Security TakeawaysTo mitigate this risk, organizations should: • Strengthen identity verification during hiring • Require multi-factor authentication across all systems • Monitor for unusual behavior from “trusted” accounts • Implement least-privilege access controls • Audit remote employee access regularly • Coordinate with HR on security-aware hiring practicesThis is a cross-functional problem — IT, Security, and HR must work together.⸻🔗 Source Articlehttps://www.nbcnews.com/investigations/north-korea-it-worker-scheme-nisos-fbi-rcna245025⸻🔗 Connect With UsIT SPARC Cast@ITSPARCCast on Xhttps://www.linkedin.com/company/sparc-sales/ on LinkedInJohn Barger@john_Video on Xhttps://www.linkedin.com/in/johnbarger/ on LinkedInLou Schmidt@loudoggeek on Xhttps://www.linkedin.com/in/louis-schmidt-b102446/ on LinkedIn
29. Redux - Node.js Security Crisis, Meta’s AI Agent Network, Nvidia’s Open Agent Platform & Oracle’s Data Center Bet
22:29||Season 2, Ep. 29Oooops. We uploaded the wrong audio. It's been fix now.In this episode of IT SPARC Cast – News Bytes, John Barger & Lou Schmidt explore four major stories shaping enterprise IT, open-source software, AI infrastructure, and the future of data centers.A new report reveals that two-thirds of Node.js installations are running outdated versions, creating major security and operational risks across modern software stacks. Meanwhile, Meta hires the creators of Moltbook, a platform designed as a social network for AI agents to communicate and collaborate.Nvidia enters the agentic AI race with plans for an open-source enterprise AI agent platform, while Oracle’s massive investments in AI data centers spark debate about whether the industry is heading toward an infrastructure bubble.From open-source sustainability to AI infrastructure strategy, this episode breaks down what these developments mean for enterprise IT leaders, developers, and technology investors. Show Notes00:00 – Intro📰 News Bytes00:43 – Two Thirds of Node.js Installations Are OutdatedA new report from the OpenJS Foundation reveals that roughly two-thirds of Node.js deployments are running outdated or end-of-life versions, creating serious security and stability concerns across modern applications.To address this, the Node.js LTS Upgrade and Modernization Program is connecting enterprises with trusted service providers audit, plan, and modernize their deployments.The initiative also helps fund open-source development by directing a portion of service revenue back to the OpenJS Foundation.https://openjsf.org/blog/nodejs-lts-upgrade-program04:59 – Meta Hires the Duo Behind MoltbookMeta has hired the creators of Moltbook, a platform designed as a collaboration network where AI agents can verify identity, exchange information, and coordinate tasks.Meta’s move suggests a strategy to become the central hub for AI agent interaction, positioning the company to support a future where large numbers of autonomous software agents perform tasks for individuals and businesses.https://www.axios.com/2026/03/10/meta-facebook-moltbook-agent-social-network10:20 – Nvidia to Launch an Open-Source AI Agent PlatformNvidia is preparing to release NemoClaw, an open-source AI agent platform designed to help enterprises deploy autonomous agents capable of automating workflows, managing data, and performing complex multi-step tasks.Key aspects of the platform include:• Enterprise-focused agent orchestration• Open-source accessibility• Compatibility beyond Nvidia hardware• Integration with major enterprise software vendorsThe move signals Nvidia’s growing interest in the agentic AI ecosystem, which could dramatically increase demand for GPU-accelerated compute infrastructure.https://www.wired.com/story/nvidia-planning-ai-agent-platform-launch-open-source/⸻14:27 – Oracle Is Building Yesterday’s Data Centers With Tomorrow’s DebtOracle is investing heavily in new AI data centers, financing much of the expansion through debt as it competes with other hyperscale cloud providers.Some analysts have raised concerns that rapid advances in AI hardware could outpace the construction timelines of new facilities, potentially creating financial risk.However, the hosts point out that building data centers requires long lead times for power infrastructure, networking, and facilities, while the compute hardware itself is typically installed later in the deployment process.The discussion highlights the importance of evaluating technology investment stories critically and considering both infrastructure realities and market narratives.https://www.cnbc.com/2026/03/09/oracle-is-building-yesterdays-data-centers-with-tomorrows-debt.html⸻20:14 – Wrap up⸻🔗 Connect With UsIT SPARC Cast@ITSPARCCast on Xhttps://www.linkedin.com/company/sparc-sales/ on LinkedInJohn Barger@john_Video on Xhttps://www.linkedin.com/in/johnbarger/ on LinkedInLou Schmidt@loudoggeek on Xhttps://www.linkedin.com/in/louis-schmidt-b102446/ on LinkedIn
29. Node.js Security Crisis, Meta’s AI Agent Network, Nvidia’s Open Agent Platform & Oracle’s Data Center Bet
22:29||Season 2, Ep. 29In this episode of IT SPARC Cast – News Bytes, John Barger & Lou Schmidt explore four major stories shaping enterprise IT, open-source software, AI infrastructure, and the future of data centers.A new report reveals that two-thirds of Node.js installations are running outdated versions, creating major security and operational risks across modern software stacks. Meanwhile, Meta hires the creators of Moltbook, a platform designed as a social network for AI agents to communicate and collaborate.Nvidia enters the agentic AI race with plans for an open-source enterprise AI agent platform, while Oracle’s massive investments in AI data centers spark debate about whether the industry is heading toward an infrastructure bubble.From open-source sustainability to AI infrastructure strategy, this episode breaks down what these developments mean for enterprise IT leaders, developers, and technology investors. 00:00 – Intro📰 News Bytes00:43 – Two Thirds of Node.js Installations Are OutdatedA new report from the OpenJS Foundation reveals that roughly two-thirds of Node.js deployments are running outdated or end-of-life versions, creating serious security and stability concerns across modern applications.To address this, the Node.js LTS Upgrade and Modernization Program is connecting enterprises with trusted service providers that can:• Audit existing deployments• Plan phased upgrades• Modernize dependencies• Maintain production stabilityhttps://openjsf.org/blog/nodejs-lts-upgrade-program04:59 – Meta Hires the Duo Behind MoltbookMeta has hired the creators of Moltbook, a platform designed as a collaboration network where AI agents can verify identity, exchange information, and coordinate tasks.Meta’s move suggests a strategy to become the central hub for AI agent interaction, positioning the company to support a future where large numbers of autonomous software agents perform tasks for individuals and businesses.https://www.axios.com/2026/03/10/meta-facebook-moltbook-agent-social-network10:20 – Nvidia to Launch an Open-Source AI Agent PlatformNvidia is preparing to release NemoClaw, an open-source AI agent platform designed to help enterprises deploy autonomous agents capable of automating workflows, managing data, and performing complex multi-step tasks.The move signals Nvidia’s growing interest in the agentic AI ecosystem, which could dramatically increase demand for GPU-accelerated compute infrastructure.https://www.wired.com/story/nvidia-planning-ai-agent-platform-launch-open-source/14:27 – Oracle Is Building Yesterday’s Data Centers With Tomorrow’s DebtOracle is investing heavily in new AI data centers, financing much of the expansion through debt as it competes with other hyperscale cloud providers.Some analysts have raised concerns that rapid advances in AI hardware could outpace the construction timelines of new facilities, potentially creating financial risk.The discussion highlights the importance of evaluating technology investment stories critically and considering both infrastructure realities and market narratives.https://www.cnbc.com/2026/03/09/oracle-is-building-yesterdays-data-centers-with-tomorrows-debt.html🔁 Wrap Up20:14 – Mail BagListener Mel asks whether laser-based networking technologies, like the TaaraConnect system discussed in a previous episode, could help improve internet access in mountainous rural areas.While line-of-sight laser connectivity could offer high speeds, weather conditions like fog and cloud cover could require backup connections such as radio or wired infrastructure.⸻🔗 Connect With UsIT SPARC Cast@ITSPARCCast on Xhttps://www.linkedin.com/company/sparc-sales/ on LinkedInJohn Barger@john_Video on Xhttps://www.linkedin.com/in/johnbarger/ on LinkedInLou Schmidt@loudoggeek on Xhttps://www.linkedin.com/in/louis-schmidt-b102446/ on LinkedIn
28. 14,000 ASUS Routers Infected: KadNap Botnet Creates Nearly Untouchable Malware Network
10:01||Season 2, Ep. 28A new malware campaign has compromised more than 14,000 ASUS routers, creating a resilient botnet that security researchers say is unusually difficult to dismantle.In this episode of IT SPARC Cast – CVE of the Week, John Barger and Lou Schmidt examine the KadNap router malware, which targets unpatched ASUS routers and installs a persistent backdoor designed to survive typical remediation efforts.The malware was identified by researchers at Lumen’s Black Lotus Labs, who discovered that infected routers are being used as part of a botnet capable of proxying internet traffic and enabling other malicious activities.Unlike many botnets that rely on centralized command servers, KadNap uses peer-to-peer control mechanisms similar to BitTorrent, making it significantly harder for security teams to disrupt.⸻🔎 What the KadNap Router Malware DoesThe malware exploits vulnerabilities in ASUS routers that have not been patched or configured securely.Once installed, KadNap: • Creates a persistent backdoor on the router • Survives reboots and firmware updates • Enables remote control of the router • Connects the device to a distributed botnet network • Routes malicious traffic through compromised residential internet connectionsResearchers also discovered the infected routers are being used by a fee-based proxy service called Doppelganger, allowing customers to route their internet traffic through unsuspecting victims’ home networks.⸻⚠ Why This Is DangerousBecause the traffic originates from compromised home routers, victims could unknowingly appear responsible for malicious activity such as: • Network attacks • Surveillance operations • Illegal browsing activity • Staging points for additional cyber intrusionsThis makes detection and attribution far more difficult.⸻🏢 Enterprise IT RiskThis vulnerability is not limited to home users.ASUS also produces small-business routers, meaning organizations or small offices using these devices could be exposed.IT professionals should also remember that compromised routers can provide attackers with a network foothold for lateral movement, especially if IoT or remote-user networks are poorly segmented.⸻🛠 How to Detect and Remove KadNapSecurity experts recommend checking routers for signs of compromise:Look for: • SSH enabled unexpectedly • Remote administration enabled • Unknown certificates or scheduled tasks • Suspicious entries in device logsBecause the malware attaches to configuration files, simply rebooting or restoring a configuration backup will not remove it.The proper remediation process: 1. Perform a full factory reset 2. Update the router firmware immediately 3. Manually reconfigure the router (do not restore backups)Experts also recommend changing default internal network ranges, such as moving away from the common 192.168.1.x subnet.⸻🔗 Source Articlehttps://arstechnica.com/security/2026/03/14000-routers-are-infected-by-malware-thats-highly-resistant-to-takedowns/⸻🔗 Connect With UsIT SPARC Cast@ITSPARCCast on Xhttps://www.linkedin.com/company/sparc-sales/ on LinkedInJohn Barger@john_Video on Xhttps://www.linkedin.com/in/johnbarger/ on LinkedInLou Schmidt@loudoggeek on Xhttps://www.linkedin.com/in/louis-schmidt-b102446/ on LinkedIn
28. Google Quantum-Proofs HTTPS, 6G Hits 1 Tbps, and Internet Over LASERS?! | IT SPARC Cast
22:19||Season 2, Ep. 28In this episode of IT SPARC Cast – News Bytes, John Barger & Lou Schmidt break down three major developments shaping the future of networking and internet infrastructure.Google begins testing a new quantum-resistant HTTPS certificate approach designed to defend the web against future quantum computing attacks. Meanwhile, Qualcomm’s CEO declares that the coming 6G mobile revolution will be essential for AI-driven applications, promising speeds up to 1 Tbps and sub-millisecond latency. Finally, TaaraConnect introduces a 25-Gbps laser-based networking system capable of delivering fiber-like speeds between buildings without laying cable.From quantum-safe encryption to AI-driven wireless networks and laser communication links, this episode explores how the next generation of connectivity will reshape enterprise IT infrastructure, data centers, and global networks. ⸻Show Notes00:00 – Intro⸻📰 News Bytes00:51 – Google Quantum-Proofs HTTPS with Compact CertificatesGoogle and Cloudflare are testing a new method to make HTTPS certificates resistant to future quantum attacks.Instead of traditional signature chains, the system uses Merkle Tree Certificates (MTCs) to dramatically shrink quantum-safe cryptographic data from roughly 15 KB down to about 700 bytes, making it practical for real-world internet use.The experiment begins with about 1,000 TLS certificates, with standards work underway through the IETF. If successful, this approach could become a foundational component of post-quantum internet security.The big unknown: how much processing overhead these new cryptographic methods will require on older client devices.https://arstechnica.com/security/2026/02/google-is-using-clever-math-to-quantum-proof-https-certificates/ ⸻05:42 – Qualcomm CEO Says the 6G Revolution Is ComingAt Mobile World Congress, Qualcomm CEO Cristiano Amon argued that the AI era will demand 6G networks, dramatically increasing bandwidth and lowering latency.Projected 6G capabilities include:• Speeds of 100 Gbps to 1 Tbps• Sub-millisecond latency• Massive connectivity for billions of devices• AI-driven network managementThe shift toward AI-heavy cloud processing means network traffic will become even more north-south oriented, sending massive datasets between edge devices and cloud infrastructure.Early 6G trials are expected around 2028, with broader deployments beginning around 2029.https://fortune.com/2026/03/03/qualcomm-ceo-resistance-is-futile-6g-mobile-revolution-approaches/⸻13:31 – TaaraConnect Uses Lasers to Deliver 25-Gbps InternetTaaraConnect is developing a laser-based point-to-point networking system capable of delivering up to 25 Gbps over distances of about 6 miles (10 km).Instead of radio waves, the system transmits data using focused beams of light, creating fiber-like connectivity without physical cables.Key features include:• Adaptive beam alignment• Automatic power adjustments during interference• Redundant beam paths to mitigate disruptions• Low-latency high-bandwidth links between buildingsWhile heavy fog remains the primary limitation, the technology could provide a powerful alternative to expensive metro fiber deployments, particularly in dense urban environments.https://newatlas.com/telecommunications/google-taara-25gbps-internet-cities-light/⸻🔁 Wrap Up19:31 – Mail BagListener Xavier shares thoughts on the rising cost of compute power and suggests that bio-AI systems using living neurons could eventually deliver superior performance-per-watt compared to traditional silicon chips.The discussion highlights a growing industry focus on compute efficiency and power consumption as data center infrastructure scales to support AI workloads.⸻🔗 Connect With UsIT SPARC Cast@ITSPARCCast on Xhttps://www.linkedin.com/company/sparc-sales/ on LinkedInJohn Barger@john_Video on Xhttps://www.linkedin.com/in/johnbarger/ on LinkedInLou Schmidt@loudoggeek on Xhttps://www.linkedin.com/in/louis-schmidt-b102446/ on LinkedIn
27. Android CVE-2026-21385: The IoT Devices IT Forgot to Patch
10:17||Season 2, Ep. 27In this episode of IT SPARC Cast – CVE of the Week, John Barger and Lou Schmidt dive into a newly exploited Android vulnerability that many IT teams may be overlooking.The issue centers around CVE-2026-21385, a high-severity vulnerability affecting Qualcomm graphics components used in Android devices. While the vulnerability requires physical access, it is actively being exploited in the wild, making it a serious concern for enterprise IT environments.But the real story isn’t smartphones.The bigger risk lies in Android devices hiding in plain sight across enterprise infrastructure — including point-of-sale terminals, warehouse scanners, embedded industrial systems, and other IoT devices that often run outdated Android versions and rarely receive timely security updates.⸻🔎 CVE-2026-21385 Overview • CVE: CVE-2026-21385 • Severity: High (CVSS 7.8) • Component: Qualcomm GPU graphics driver used in Android • Exploit Status: Actively exploited in the wild • Access Required: Physical access • Patch: Included in March 2026 Android Security BulletinSeveral additional vulnerabilities were also patched in the same release, including critical Android framework remote code execution flaws, increasing the urgency for organizations to deploy updates wherever possible.⸻⚠ Why Enterprise IT Should CareMost organizations focus on employee phones when thinking about Android security.However, the real exposure often comes from embedded Android devices that organizations forget about:Common examples include: • Point-of-sale payment terminals • Warehouse inventory scanners (Zebra, Honeywell, etc.) • Retail handheld devices • Industrial control panels • Vehicle infotainment systems running Android • Embedded tablets in appliances or machineryMany of these devices: • Run older Android versions • Receive delayed or nonexistent updates • Expose USB or physical ports that could enable exploitation • Are connected to internal networksIf compromised, these systems could become the first step in a lateral network attack.⸻🔐 Key Security TakeawaysOrganizations should treat this vulnerability as a wake-up call for Android-based IoT security.Recommended actions: • Inventory all Android-based devices in your environment • Identify IoT or embedded Android systems • Verify whether vendors provide security updates • Push vendors for timelines if patches are not available • Segregate IoT devices onto isolated networks • Lock down physical access and exposed USB portsIgnoring embedded Android devices can create a hidden attack path directly into corporate networks.⸻💬 Listener FeedbackFollowing last week’s episode discussing the Conduent ransomware breach, listeners shared their experiences receiving breach notification letters.One listener reported receiving a notification despite not participating in government assistance programs, while another reported being impacted through health insurance providers like Blue Cross Blue Shield.The scope of the Conduent breach appears to be continuing to expand, reinforcing the importance of monitoring vendor supply-chain exposure.⸻🔗 Connect With UsIT SPARC Cast@ITSPARCCast on Xhttps://www.linkedin.com/company/sparc-sales/ on LinkedInJohn Barger@john_Video on Xhttps://www.linkedin.com/in/johnbarger/ on LinkedInLou Schmidt@loudoggeek on Xhttps://www.linkedin.com/in/louis-schmidt-b102446/ on LinkedIn
27. Anthropic Drops Safety Pledge, Open Source Security Crisis & OpenAI’s Compute Crunch
21:19||Season 2, Ep. 27In this episode of IT SPARC Cast – News Bytes, John Barger and Lou Schmidt break down three major stories shaping the future of AI, enterprise infrastructure, and software security.Anthropic revises its flagship AI safety pledge amid competitive pressure, open source registries warn they lack funding for basic security protections, and OpenAI scrambles for compute power as large-scale infrastructure plans stall.From AI governance and supply chain risk to infrastructure bottlenecks and power constraints, this episode explores what enterprise IT leaders need to be watching right now.⸻⏱️ Show Notes00:00 – IntroAnthropic revises its safety framework, open source ecosystems struggle to fund security, and OpenAI races to secure compute capacity as infrastructure constraints tighten across the AI industry.⸻📰 News Bytes⸻00:44 – Anthropic Drops Flagship Safety PledgeAnthropic has revised its 2023 Responsible Scaling Policy, removing its categorical commitment to halt training if safety guarantees could not be ensured in advance. The company says the shift reflects rapid AI advancement, competitive pressures, and the need for transparency over unilateral restrictions.John and Lou unpack what this means for enterprise deployments: Is this a rollback of safety? Or a move toward operational flexibility and published risk roadmaps? The bigger issue may be how AI vendors balance guardrails, customer control, and competitive pressure.https://time.com/7380854/exclusive-anthropic-drops-flagship-safety-pledge/ ⸻08:16 – Open Source Registries Can’t Afford Basic SecurityMajor open source ecosystems such as PyPI, npm, RubyGems, and others are reportedly facing funding shortfalls that threaten their ability to implement fundamental security protections.With supply chain attacks on the rise and AI accelerating code generation, underfunded registries present a growing enterprise risk. The hosts discuss why “free” does not mean costless — and why corporate IT teams must contribute financially or through engineering resources to sustain the security of the tools they depend on.https://www.theregister.com/2026/02/16/open_source_registries_fund_security/ ⸻12:36 – Inside OpenAI’s Scramble to Secure Compute After Stargate StalledOpenAI’s large-scale infrastructure plans have reportedly slowed, forcing the company to seek alternative compute sources to sustain AI growth.The episode explores the real bottlenecks: wafer starts, power generation, turbines, construction capacity, data center labor, and capital coordination. With AI revenue tightly correlated to compute availability, infrastructure constraints may be the biggest story in AI for 2026 and beyond.https://www.theinformation.com/articles/inside-openais-scramble-get-computing-power-stargate-stalled ⸻🔁 Wrap Up19:15 – Mail BagListener Xavier highlights how surface-level headlines often hide deeper enterprise implications — a reminder that IT leaders must look beneath the story to understand downstream risk and opportunity.20:36 – Wrap UpFrom AI safety governance and competitive pressure to supply chain funding gaps and compute shortages, Episode 27 reinforces one theme: infrastructure, transparency, and long-term planning now define enterprise AI strategy.⸻🔗 Connect With UsIT SPARC Cast@ITSPARCCast on Xhttps://www.linkedin.com/company/sparc-sales/ on LinkedInJohn Barger@john_Video on Xhttps://www.linkedin.com/in/johnbarger/ on LinkedInLou Schmidt@loudoggeek on Xhttps://www.linkedin.com/in/louis-schmidt-b102446/ on LinkedIn
26. Anthropic vs. The Pentagon, HDD Sellout 2026, and Copilot’s Confidential Email Bug
18:44||Season 2, Ep. 26In this episode of IT SPARC Cast – News Bytes, John Barger & Lou Schmidt unpack three stories that expose the real friction points in enterprise IT: AI ethics in defense contracts, looming hardware shortages, and data governance risks in Microsoft Copilot.Anthropic and the Pentagon clash over Claude’s military use, Western Digital reports zero remaining HDD capacity for 2026, and Microsoft confirms a Copilot bug that summarized confidential emails. From supply chain strategy to SaaS risk management, this episode highlights why enterprise IT leaders must think beyond features and focus on contracts, capacity, and control.⸻⏱️ Show Notes00:00 – IntroHard drive shortages, AI contract battles, and Copilot privacy concerns headline a week that reinforces one theme: control over infrastructure and software matters more than ever.⸻📰 News Bytes00:46 – Anthropic and the Pentagon Are Reportedly Arguing Over Claude UsageAnthropic pushes back against unrestricted military use of Claude AI, raising ethical, contractual, and operational questions. The Pentagon may reconsider its $200M relationship, exposing a major risk for organizations deploying AI: what happens when vendor policies change after integration?https://techcrunch.com/2026/02/15/anthropic-and-the-pentagon-are-reportedly-arguing-over-claude-usage/ ⸻07:19 – Western Digital Has No More HDD Capacity Left for 2026Western Digital reports its entire 2026 hard drive production is already spoken for. Similar signals from Seagate suggest storage pricing pressure is imminent. The hosts explain why this isn’t just about spinning disks—it’s about AI data center demand driving up costs across RAM, SSDs, GPUs, and enterprise hardware.https://wccftech.com/western-digital-has-no-more-hdd-capacity-left-out/ ⸻12:06 – Microsoft Says Bug Causes Copilot to Summarize Confidential EmailsMicrosoft confirms a Copilot bug that processed confidential emails stored in drafts and sent folders, despite policy settings meant to block them. Although no data reportedly left the organization, the incident underscores governance, SaaS dependency, and AI access-control risks enterprises must plan for.https://www.bleepingcomputer.com/news/microsoft/microsoft-says-bug-causes-copilot-to-summarize-confidential-emails/ ⸻🔁 Wrap Up16:42 – Mail BagListener Dennis drops a Back to the Future “jigawatt” reference, and Xavier reinforces the importance of AI security hygiene and fine-grained permission management.17:52 – Wrap UpFinal thoughts on vendor lock-in, AI policy control, supply chain modeling, and why IT leaders need stronger collaboration with finance and legal teams.⸻🔗 Connect With UsIT SPARC Cast@ITSPARCCast on Xhttps://www.linkedin.com/company/sparc-sales/John Barger@john_Video on Xhttps://www.linkedin.com/in/johnbarger/Lou Schmidt@loudoggeek on Xhttps://www.linkedin.com/in/louis-schmidt-b102446/